Overview
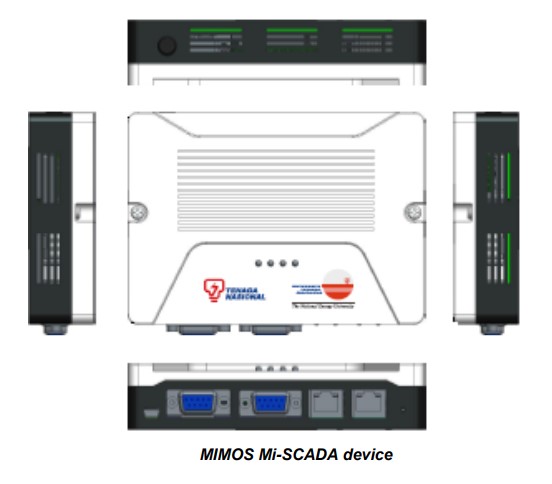
MIMOS Supervisory Control and Data Acquisition (Mi-SCADA) is a control system used to monitor and control a plant or equipment in industries such as energy, water and waste control, oil and gas refining, transportation and telecommunications. Mi-SCADA provides end-to-end authentication and encryption to protect the SCADA link from unauthorised access and control, eavesdropping and malicious attacks.
MIMOS Mi-SCADA is a bump-in-the-wire device, which allows
easy and seamless integration into an existing system to enable an ultimate security protection over the SCADA network. With the powerful SHA-256/384, AES-128/256 and the proprietary Mi-CRYPT-128/256, together with the lightweight cryptography tool suites i.e. PRESENT and PHOTON, Mi-SCADA can be configured to meet the different security strength and throughput performance requirements of the target system.
Features
- Comprehensive security suites
- Supports multiple SCADA protocols
- User configurable
Technology Benefits
- Bump-in-the-wire
- Device-based authentication
- End-to-end encryption
- Strong assurance of authenticity
- Proprietary encryption algorithm
Mi-SCADA comprises the following features:
Features
Mi-SCADA comprises the following features:
- Comprehensive Security Suites
Encryption : AES-128/256
Mi-CRYPT-128/256
PRESENT
Hash : SHA-256/384
PHOTON
Key Exchange : ECDH P-384
Digital Signature : ECDSA P-384 - Supports Multiple SCADA Protocols
Able to support IEC-101 (Serial) and IEC-104 (Ethernet) industrial standard SCADA protocols. - User Configurable
Allows user configuration to meet different system requirements
Technology Benefits
The main impacts of Mi-SCADA are:
- Bump-in-the-Wire
Allows seamless integration into existing system. - Device-Based Authentication
Validates user’s right to access to the Mi-SCADA system. - End-to-End Encryption
Prevents eavesdropping and ensure confidentiality. - Strong Assurance of Authenticity
Avoids intentional, unauthorised modification of the data. - Proprietary Encryption Algorithm
Enables extra layer of security implying “security through obscurity”.